Tech
264.68.111.161: The Mystery of an Invalid IP Deep Dive Guide

Introduction
At first glance, 264.68.111.161 looks like any other standard IPv4 address. It carries the familiar four-octet structure separated by periods, giving the impression of technical legitimacy. Yet beneath that surface lies a subtle but critical flaw. The number 264 exceeds the maximum value allowed in IPv4 addressing, immediately rendering the entire string invalid. Still, 264.68.111.161 continues to appear in logs, online discussions, configuration errors, and even security reports. Why does an address that cannot exist in real-world networking environments continue to surface? The answer opens a fascinating window into how the internet works, how systems interpret data, and how small mistakes can ripple through digital infrastructure in unexpected ways.
Understanding 264.68.111.161 requires stepping back and examining the architecture of IPv4 itself. Only then can we appreciate why this address is technically impossible and why its appearance is more meaningful than it seems.
Understanding IPv4 Structure and Its Mathematical Limits
The foundation of modern internet communication rests on IP addressing. IPv4, the fourth version of the Internet Protocol, uses a 32-bit numerical system divided into four octets. Each octet can represent a value from 0 to 255. This limitation exists because each octet contains eight bits, and eight bits can only represent 256 unique values. When we see an address such as 192.168.1.1, each segment sits comfortably within that 0–255 range.
READ MORE: The Cultural Evolution and Influence of daylin ryder
The first segment of 264.68.111.161 immediately breaks this rule. Since 264 is greater than 255, the address falls outside the allowable range defined by the IPv4 standard. This means it cannot be assigned to a device, cannot be routed across networks, and cannot exist within any properly configured internet infrastructure.
What makes this interesting is not merely that 264.68.111.161 is invalid, but that systems sometimes still record it. This tells us something important about how software processes inputs. Many applications log what they receive before validating it. That means even an impossible IP address can be preserved in system records if it was submitted through a form, embedded in a request header, or generated by malformed data.
Why Invalid IP Addresses Appear in Real Systems
You might assume that invalid addresses like 264.68.111.161 would simply be rejected and forgotten. In practice, that is not always the case. There are several scenarios in which such an address can appear.
One common cause is user error. A person manually typing an IP address might accidentally enter 264 instead of 246 or 192. Since the digits look plausible, the mistake can pass unnoticed until validation occurs. If the system logs raw input before validation, the invalid entry remains recorded.
Another frequent cause is automated bot traffic. Scripts that probe websites for vulnerabilities often generate randomized IP headers. Some of these scripts do not strictly conform to IPv4 standards, resulting in impossible addresses like 264.68.111.161 appearing in server logs.
Data corruption can also play a role. When information is transferred between systems with incompatible encoding or formatting rules, numbers may shift unexpectedly. An originally valid octet could be altered during parsing, producing a mathematically impossible result.
There is also the possibility of deliberate spoofing attempts. Attackers sometimes manipulate header fields in network requests. While routers will not forward traffic from an invalid address, certain application-layer logs may still record the spoofed value before it is discarded.
The Security Implications of 264.68.111.161
At first glance, an invalid IP address may seem harmless. After all, it cannot route traffic. However, its presence in logs can signal deeper issues.
If 264.68.111.161 appears repeatedly in server records, it may indicate that validation routines are weak or improperly implemented. Systems should ideally reject malformed addresses before they reach application-level processing. If they do not, it opens the door to other forms of malformed input slipping through.
Invalid IP entries can also complicate forensic investigations. Security analysts often rely on log accuracy to trace suspicious activity. When impossible addresses like 264.68.111.161 appear, they introduce noise into datasets. Analysts must then determine whether the entry is simply a typo, corrupted data, or part of a broader probing attempt.
There is also a subtle psychological factor. Novice administrators encountering 264.68.111.161 might assume it represents a foreign or obscure network. Without understanding IPv4 constraints, they could waste time investigating something that mathematically cannot exist.
IPv4 Exhaustion and the Context of Numerical Boundaries
The existence of 264.68.111.161 becomes even more interesting when placed against the backdrop of IPv4 exhaustion. Over the past decade, available IPv4 addresses have been largely allocated, prompting the global transition toward IPv6. IPv6 expands addressing capacity dramatically, allowing for vastly larger numerical ranges.
However, IPv6 formatting is entirely different, using hexadecimal notation and colon separators. An address like 264.68.111.161 does not belong to IPv6 either. It occupies a conceptual gray area, resembling IPv4 while violating its rules and lacking the structure of IPv6.
This boundary violation highlights a broader truth about digital systems: they depend on strict mathematical definitions. Once those definitions are exceeded, the address ceases to function within the network’s logic. The internet is remarkably flexible in many ways, but its core protocols remain rigid in their numeric boundaries.
Logging Systems and the Persistence of Bad Data
Modern web servers, firewalls, and cloud platforms generate enormous volumes of logs. These logs often capture raw request headers before applying validation filters. As a result, 264.68.111.161 can be stored even if it was never routable.
In some cases, load balancers and reverse proxies add forwarding headers that include client IP information. If a malicious or misconfigured client inserts 264.68.111.161 into those headers, downstream systems may record it without verifying its authenticity.
This persistence of invalid data demonstrates a broader lesson in system design. Input validation should occur as early as possible in the processing chain. When invalid inputs pass through multiple layers, they increase the risk of unexpected behavior or analytical confusion.
Educational Value of an Impossible Address
Strangely enough, 264.68.111.161 serves as a useful teaching tool. Networking students often learn IPv4 theory abstractly, but seeing a concrete example of an invalid address reinforces the concept of octet limits.
It encourages deeper understanding rather than rote memorization. Instead of simply remembering that each octet must be between 0 and 255, students confronted with 264.68.111.161 must reason through why 264 exceeds the allowable range. That reasoning strengthens their grasp of binary representation and subnetting fundamentals.
In cybersecurity training environments, instructors sometimes introduce malformed data to test analytical awareness. Recognizing that 264.68.111.161 cannot exist demonstrates attention to detail and technical literacy.
Misinterpretations and Online Confusion
Online forums occasionally feature discussions about 264.68.111.161, with some users speculating that it might belong to a hidden network, a classified infrastructure, or a new protocol extension. Such speculation arises from misunderstanding.
The internet’s architecture is governed by internationally coordinated standards. Any valid IPv4 address must comply with defined numerical boundaries. There are reserved ranges, private ranges, and special-use blocks, but none permit an octet value beyond 255.
The persistence of questions about 264.68.111.161 reveals how easily numeric patterns can appear authoritative. Many people assume that if something looks technical, it must be valid. Critical thinking, however, demands verification against known constraints.
Broader Lessons About Data Integrity
Beyond networking theory, 264.68.111.161 symbolizes a broader principle in computing: not all structured data is valid data. Systems frequently receive input that appears formatted correctly but violates underlying rules.
This distinction matters profoundly in software development. Validation cannot rely solely on superficial structure. A string matching the pattern “number.number.number.number” is not necessarily a legitimate IPv4 address. Each number must also satisfy defined numeric limits.
When developers overlook such constraints, vulnerabilities can emerge. Improper validation has historically contributed to injection attacks, buffer overflows, and logic errors. While 264.68.111.161 itself may not be dangerous, the mindset that allows it to pass unchecked can create risk.
Could 264.68.111.161 Ever Become Valid?
Theoretically, one might wonder whether protocol changes could someday permit larger octet values. In practical terms, this is extraordinarily unlikely. IPv4’s 32-bit structure is deeply embedded in hardware, firmware, and global infrastructure. Altering the maximum octet value would require redefining the entire protocol.
Instead, the internet’s evolution has taken a different path through IPv6 adoption. IPv6 does not expand octet limits but replaces the entire format with a 128-bit addressing scheme. Therefore, 264.68.111.161 will remain invalid under IPv4 rules and irrelevant under IPv6 rules.
This permanence underscores how foundational design decisions shape decades of technological development. Numeric boundaries chosen in the early days of networking continue to define what is possible today.
Conclusion
264.68.111.161 may appear at first glance to be just another technical string, but its impossibility tells a compelling story. It illustrates the strict mathematical structure underlying IPv4, highlights the importance of rigorous input validation, and reveals how malformed data can persist in logs and discussions. Its repeated appearance in digital records reflects not a hidden network or secret allocation, but the simple reality that systems sometimes record what they receive before judging its validity.
In a broader sense, 264.68.111.161 serves as a reminder that technology operates within clearly defined boundaries. When those boundaries are crossed, functionality collapses. Yet the traces left behind can still teach us valuable lessons about system design, cybersecurity awareness, and the discipline required to maintain data integrity. What seems like a trivial error becomes, upon closer examination, a powerful demonstration of how the internet’s architecture enforces order through mathematics.
FAQs
What is 264.68.111.161?
264.68.111.161 is an invalid IPv4 address because the first octet exceeds the maximum allowable value of 255. It cannot exist within standard internet routing systems.
Why does 264.68.111.161 sometimes appear in server logs?
It may appear due to user input errors, automated bot activity, spoofed request headers, or systems logging raw data before validating it.
Can 264.68.111.161 be assigned to a device?
No, it cannot be assigned to any device because IPv4 addressing strictly limits each octet to values between 0 and 255.
Is 264.68.111.161 related to IPv6?
No, IPv6 uses a completely different hexadecimal format separated by colons. 264.68.111.161 does not fit IPv6 standards either.
Does the appearance of 264.68.111.161 indicate a security breach?
Not necessarily. While it can be associated with malformed or spoofed requests, its presence alone usually indicates invalid input rather than a confirmed security incident.
Tech
RWU UAR: The Complete Guide to the Role-Weighted User Unified Access and Resources Framework, Undergraduate Academic Research, and Modern Institutional Systems
Tech
Inflatom: Emerging Buzzword, Smart Tech Concept, Physics Mashup, and Cultural Phenomenon

What Is Inflatom? Understanding the 2026 Buzzword
If you’ve recently come across the term Inflatom, you’re not alone—and no, it’s not officially in the dictionary (yet). Still, in 2026, it’s gaining serious traction across tech blogs, business discussions, and futuristic think pieces. So what exactly does it mean?
At its core, Inflatom is a blended word (portmanteau) combining “inflation” (rising prices or expansion) and “inflaton” (a theoretical field in physics responsible for the rapid expansion of the universe after the Big Bang). Sounds complex? It is—but that’s also what makes it fascinating.
In everyday usage, Inflatom represents the idea of controlled expansion in a rapidly changing world. Whether it’s applied to business automation, personal finance, or even abstract philosophical thinking, the term captures a very 2026 mindset: grow fast, but stay smart and balanced.
Unlike traditional terms with fixed meanings, Inflatom is fluid and context-driven. In one article, it might describe an AI-powered system that adjusts pricing in real time. In another, it might symbolize how individuals navigate rising living costs. And in more speculative spaces, it becomes a cosmic metaphor for the forces driving modern society forward.
What makes this term stand out is how well it reflects the current moment. We’re living in an era defined by automation, economic uncertainty, and rapid technological growth. Inflatom wraps all of that into a single, catchy concept, making it both intriguing and highly shareable.
The Origins of Inflatom: Where Did It Come From?

Inflatom
Like many modern buzzwords, Inflatom didn’t emerge from academia or official institutions. Instead, it grew organically through online content, creative writing, and marketing language. By early 2026, it started appearing in blog posts with headlines like “The Future of Smart Growth: Enter Inflatom” or “Inflatom Explained: The Hidden Force Behind Modern Expansion.”
The word’s foundation comes from two powerful ideas:
- Inflation, a term every American is familiar with, especially after years of fluctuating prices affecting groceries, housing, and energy.
- Inflaton, a concept from cosmology describing the force that caused the universe to expand exponentially in its earliest moments.
By combining these, writers created something that feels both scientific and practical, even if it’s not technically defined. It’s the kind of term that sounds credible enough to spark curiosity—and vague enough to be used in multiple contexts.
Interestingly, there is a real company called Inflatom APS in Norway, established years ago. However, there’s no strong evidence linking it directly to the recent surge in popularity. Most of the buzz comes from content creators and marketers experimenting with new language to describe complex trends.
This origin story highlights something important: in 2026, language evolves online faster than ever. Words don’t need official approval to gain traction—they just need to resonate.
Inflatom as a Smart Automation System
One of the most practical interpretations of Inflatom is as a smart automation system. In this context, it refers to technology that can monitor, adjust, and optimize processes in real time without human intervention.
Imagine running a business where prices automatically adjust based on demand, inventory levels update themselves, and workflows reorganize to maximize efficiency. That’s the kind of system people describe when they talk about Inflatom in a tech sense.
For example, a retailer might use an Inflatom-style system to:
- Adjust product prices dynamically during periods of high inflation
- Optimize supply chains to reduce waste
- Automatically allocate resources where they’re needed most
In homes, similar ideas apply. Smart devices already adjust temperature, lighting, and energy usage based on behavior. The Inflatom concept takes this further, suggesting a future where everything is continuously optimized for balance and efficiency.
This idea is especially appealing in 2026 because of the rise of AI-driven tools. People are increasingly looking for ways to simplify complex decisions, and Inflatom represents that desire for hands-off, intelligent control.
Inflatom in Economics: Rethinking Value in an Inflationary World
Another powerful angle of Inflatom comes from the world of economics. Here, it’s used to describe a more granular way of understanding inflation and value—almost like breaking things down into their smallest measurable units.
Think of it as analyzing the “atomic level” of money. Instead of just looking at overall inflation rates, the Inflatom concept encourages people to focus on how price changes affect individual transactions, daily purchases, and personal budgets.
In 2026, this approach feels especially relevant. While inflation has cooled compared to previous years, it still impacts everyday life. Groceries, rent, and utilities may not be skyrocketing anymore, but they’re still higher than many people would like.
Using an Inflatom mindset, individuals and businesses can:
- Track micro-level spending patterns
- Identify where inflation hits hardest
- Adjust habits or pricing strategies accordingly
For example, a small business owner might notice that ingredient costs have increased slightly across multiple items. Instead of raising all prices equally, they could make targeted adjustments, maintaining customer trust while protecting profit margins.
This perspective turns inflation from a vague, overwhelming concept into something manageable and actionable.
Inflatom as a Physics-Inspired Metaphor
Now here’s where things get really interesting. Some writers use Inflatom as a metaphor inspired by physics, specifically the concept of the inflaton field—the force believed to have driven the universe’s rapid expansion after the Big Bang.
In this context, Inflatom represents the invisible forces driving growth in modern society. Technology, data, innovation—these are the “fields” pushing everything forward at an incredible pace.
But just like in cosmology, rapid expansion comes with risks. Without control, it can lead to instability, imbalance, or collapse. That’s why the Inflatom concept often includes an element of regulation or balance.
It’s a poetic way of describing the world we live in:
- Startups scaling overnight
- AI transforming industries
- Economies expanding and contracting
All of these can be seen as part of a larger “Inflatom force” shaping the future.
Why Inflatom Is Trending in 2026
So why is Inflatom suddenly everywhere? The answer lies in timing. The term perfectly aligns with several major trends shaping 2026:
- Ongoing concerns about inflation and economic stability
- Rapid growth in AI and automation technologies
- A cultural shift toward simplifying complex systems
- The internet’s love for catchy, futuristic buzzwords
People are looking for ways to understand a world that feels both fast-moving and unpredictable. Inflatom offers a simple label for a very complex reality, which makes it highly shareable.
It also helps that the word sounds futuristic. It feels like something out of a sci-fi novel, which gives it an extra layer of appeal in tech and innovation circles.
Real-World Applications of the Inflatom Concept
Even though Inflatom isn’t a formal system, its ideas are already being applied in real life. You can see it in tools and strategies that focus on automation, adaptability, and efficiency.
For individuals, this might mean using apps that:
- Automatically adjust budgets and savings goals
- Optimize investment portfolios based on market conditions
- Track spending in real time
For businesses, it could involve:
- AI-driven pricing algorithms
- Automated inventory management systems
- Data-driven decision-making tools
In each case, the goal is the same: respond to change بسرعة and intelligently without constant manual input.
Challenges and Criticism of the Inflatom Idea
Of course, not everyone is sold on Inflatom. Critics argue that it’s just another buzzword without a clear definition, used to make ordinary ideas sound more innovative than they really are.
There’s some truth to that. Many concepts associated with Inflatom—like automation and data optimization—already exist. The term itself doesn’t introduce new technology; it simply repackages existing ideas in a more جذاب way.
There’s also the risk of over-automation. Relying too heavily on systems that adjust everything automatically can lead to loss of control or unexpected outcomes, especially if the data driving those decisions is flawed.
So while Inflatom is a useful concept, it’s important to approach it with a balanced perspective.
The Future of Inflatom: Trend or Lasting Concept?
Will Inflatom still be relevant in a few years? That’s hard to predict. Some internet-born terms fade quickly, while others evolve into widely accepted concepts.
There are a few possible outcomes:
- It becomes a recognized business or tech term
- It gets adopted as a brand name or product category
- Or it fades away as another short-lived trend
Regardless of what happens, the ideas behind it—smart growth, automation, and balance—are here to stay.
Conclusion: Why Inflatom Matters in 2026
Inflatom captures the essence of modern life: rapid growth paired with the need for control. Whether you see it as a tech concept, an economic framework, or a creative metaphor, it reflects the challenges and opportunities of our time.
In a world where everything is expanding—data, technology, economies—the real challenge isn’t growth itself, but managing it wisely. And that’s exactly what Inflatom is all about.
FAQs About Inflatom
1. Is Inflatom a real word?
No, it’s a modern buzzword, not officially recognized in dictionaries.
2. What does Inflatom mean?
It refers to smart, controlled growth, combining ideas from inflation and physics.
3. Is Inflatom a technology?
Not exactly—it’s more of a concept, though it relates to automation systems.
4. Why is Inflatom popular in 2026?
Because it reflects trends in AI, inflation, and rapid innovation.
5. Can I use Inflatom in business or content?
Yes, it’s often used as a creative or branding term to describe modern growth strategies.
Tech
Chromtex: Sustainable Textile Chemicals, High-Performance Fabrics, and Eco-Friendly Innovation Explained

The textile industry in 2026 is undergoing a major transformation, driven by sustainability demands, stricter environmental regulations, and the need for high-performance fabrics. At the center of this evolution is Chromtex, a brand increasingly recognized for combining advanced textile chemistry with eco-conscious innovation. From pretreatment to dyeing and finishing, Chromtex provides solutions that not only improve fabric quality but also reduce environmental impact.
This in-depth guide explores everything about Chromtex in 2026, including its technologies, product range, sustainability commitments, industry applications, and why it is becoming a preferred partner for modern textile manufacturers worldwide.
What Is Chromtex? Brand Overview and Core Philosophy
Chromtex is a specialized name in the textile sector, representing a blend of “chroma” (color) and “tex” (textiles). This reflects its core strength—enhancing fabric performance through advanced color chemistry and processing technologies.
In 2026, Chromtex stands for more than just textile chemicals. It represents a complete ecosystem of solutions designed to improve:
- Fabric durability
- Color vibrancy and fastness
- Process efficiency
- Environmental sustainability
What sets Chromtex apart is its philosophy of “performance meets responsibility.” Instead of focusing solely on aesthetics or cost, the brand emphasizes long-lasting textiles that minimize waste and environmental harm.
Modern consumers demand clothing and materials that are not only stylish but also sustainable. Chromtex helps manufacturers meet this demand by offering clean-label textile solutions that align with global sustainability goals.
Origins and Evolution of Chromtex in the Textile Industry
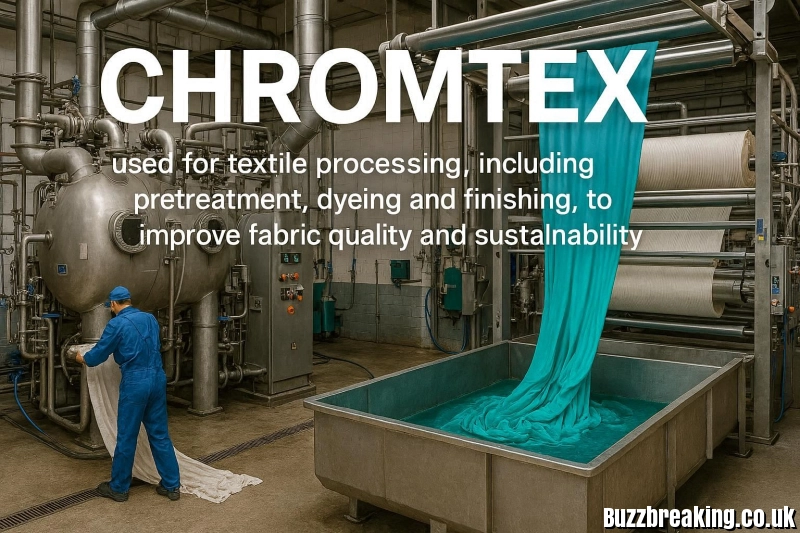
Chromtex
Chromtex emerged as a response to growing concerns about pollution in textile manufacturing, particularly in dyeing and finishing processes. Traditionally, textile production has been one of the most resource-intensive industries, consuming large amounts of water, energy, and chemicals.
As regulations tightened globally—especially in Europe and Asia—there was a clear need for safer, more efficient alternatives. Chromtex capitalized on this shift by developing low-impact chemical formulations that reduce environmental harm without compromising performance.
By 2026, the brand has evolved into a comprehensive textile solutions provider, supporting industries ranging from fashion to technical textiles. Its growth is closely tied to trends such as:
- Circular economy practices
- Traceability in supply chains
- Demand for eco-certified materials
Chromtex’s ability to adapt and innovate has made it a key player in the future of sustainable textiles.
Core Technologies: Pretreatment, Dyeing, and Finishing Solutions
Chromtex’s strength lies in its expertise across the three main stages of textile processing:
Pretreatment Technologies
Pretreatment prepares raw fabrics for dyeing by removing impurities. Chromtex offers:
- Enzyme-based scouring agents
- Low-temperature wetting agents
- Eco-friendly desizing solutions
These reduce water and energy usage while improving fabric absorbency.
Dyeing Innovations
Dyeing is traditionally one of the most polluting stages. Chromtex addresses this with:
- High-fixation dyes that minimize waste
- Low-temperature dyeing systems
- Leveling agents for uniform color distribution
The result is brighter colors with less environmental impact.
Finishing Solutions
Finishing adds functional properties to fabrics. Chromtex provides:
- Softeners for improved feel
- Water-repellent and stain-resistant coatings
- Antimicrobial treatments
These enhance both comfort and performance, making fabrics suitable for demanding applications.
Sustainable Textile Chemicals: Eco-Friendly Innovation
Sustainability is at the heart of Chromtex’s operations. In 2026, the brand focuses on creating textile chemicals that are safe, efficient, and environmentally responsible.
Key sustainability features include:
- Biodegradable formulations
- Reduced chemical toxicity
- Lower water consumption during processing
- Energy-efficient production methods
Chromtex also aligns with global initiatives such as:
- ZDHC (Zero Discharge of Hazardous Chemicals)
- REACH compliance
- OEKO-TEX certification standards
By adopting these practices, manufacturers using Chromtex can significantly reduce their environmental footprint while maintaining high-quality output.
High-Performance Fabrics Enabled by Chromtex
Chromtex doesn’t just improve processes—it enhances the final product itself. Fabrics treated with Chromtex solutions offer a range of advanced features:
- Enhanced durability and abrasion resistance
- Long-lasting color retention
- Moisture-wicking and breathability
- UV protection and flame resistance
- Antimicrobial and odor-control properties
In 2026, these features are especially important in sectors like sportswear, healthcare, and automotive textiles, where performance is critical.
Some advanced developments even include smart textiles, where fabrics can regulate temperature or integrate with wearable technology.
Key Product Ranges and Solutions in 2026
Chromtex offers a diverse portfolio tailored to different textile needs. Its main product categories include:
Pretreatment Series
Designed for cotton, polyester, and blended fabrics, these products ensure clean, absorbent materials ready for dyeing.
Dyeing Auxiliaries
Optimized for various dye types, these solutions improve color consistency and reduce waste.
Finishing Agents
These include softeners, wrinkle-resistant coatings, and functional finishes that enhance fabric usability.
Specialty Solutions
Chromtex also provides chemicals for:
- Digital textile printing
- Pigment systems
- Technical textiles
The 2026 lineup emphasizes bio-based ingredients and low-impact formulations, reflecting the brand’s sustainability focus.
Applications Across Industries
Chromtex solutions are used across a wide range of industries, highlighting their versatility.
Fashion and Apparel
Brands use Chromtex to create long-lasting, vibrant garments that meet sustainability standards.
Healthcare Textiles
Hospitals require fabrics with antimicrobial properties and durability, making Chromtex an ideal choice.
Automotive Industry
Car interiors benefit from UV-resistant, stain-proof, and flame-retardant textiles.
Technical and Industrial Textiles
Applications include:
- Protective clothing
- Geotextiles
- Sports and performance wear
Home Textiles
From bedding to upholstery, Chromtex enhances comfort, longevity, and functionality.
This broad applicability makes Chromtex a multi-industry solution provider.
Chromtex vs Traditional Textile Chemicals
When compared to conventional textile chemicals, Chromtex offers several clear advantages.
| Feature | Traditional Chemicals | Chromtex Solutions |
|---|---|---|
| Environmental Impact | High pollution | Low-impact, eco-friendly |
| Energy Use | High ताप | Reduced ताप processes |
| Dye Fixation | Lower efficiency | High fixation rates |
| Fabric Quality | Standard | Enhanced performance |
| Compliance | Often limited | Meets global standards |
These improvements translate into cost savings, better product quality, and easier regulatory compliance.
Sustainability Certifications and Industry Compliance
In 2026, certifications are crucial for textile brands. Chromtex supports compliance with major global standards:
- OEKO-TEX Standard 100
- GOTS (Global Organic Textile Standard)
- Bluesign® system
- ZDHC guidelines
These certifications ensure that fabrics are safe for consumers and environmentally responsible.
Chromtex also promotes transparency and traceability, helping brands build trust with eco-conscious consumers.
Latest Innovations and 2026 Developments
Chromtex continues to push boundaries with new technologies. Recent innovations include:
- Next-generation enzyme blends for faster pretreatment
- Fluorocarbon-free water repellents
- Low-impact pigment dispersions
- Digital tools for process optimization
In 2026, digitalization plays a major role. Chromtex offers tools that allow manufacturers to:
- Monitor chemical usage
- Optimize recipes in real time
- Track sustainability metrics
This integration of technology and chemistry sets Chromtex apart from traditional competitors.
Future Outlook: Chromtex and the Next Era of Textiles
The future of textiles is moving toward sustainability, innovation, and smart functionality—and Chromtex is well-positioned to lead this transformation.
Key trends shaping its future include:
- AI-driven textile processing
- Expansion of bio-based chemicals
- Growth of circular textile systems
- Integration with wearable technology
As global demand for sustainable products increases, Chromtex is expected to play a crucial role in helping manufacturers achieve net-zero goals.
Conclusion
Chromtex in 2026 represents the future of textile innovation, where performance and sustainability go hand in hand. By offering advanced solutions for pretreatment, dyeing, and finishing, the brand enables manufacturers to create high-quality, eco-friendly fabrics that meet modern demands.
From fashion to healthcare and industrial applications, Chromtex is redefining what textiles can achieve. Its commitment to clean chemistry, efficiency, and innovation makes it a trusted partner in a rapidly evolving industry.
For businesses looking to stay competitive while embracing sustainability, Chromtex provides not just products—but a complete pathway to responsible textile production.
FAQs
1. What is Chromtex used for?
Chromtex is used for textile processing, including pretreatment, dyeing, and finishing, to improve fabric quality and sustainability.
2. Is Chromtex environmentally friendly?
Yes, Chromtex focuses on eco-friendly, biodegradable, and low-impact chemical solutions.
3. Which industries use Chromtex products?
Industries include fashion, healthcare, automotive, home textiles, and technical textiles.
4. What makes Chromtex different from traditional chemicals?
It offers higher efficiency, lower environmental impact, and better fabric performance.
5. Are Chromtex products certified?
Yes, they align with standards like OEKO-TEX, GOTS, and ZDHC compliance.
-

 FOODs1 week ago
FOODs1 week agoγουακαμε: The Ultimate Guide to Authentic Guacamole, Tips & Modern Twists
-

 Blogs3 days ago
Blogs3 days agoBetfairplay777.com: Complete 2026 Guide to Features, Games, and Betting Markets
-

 Blogs1 week ago
Blogs1 week agoFraudee: Why Experts Say Stop Using the Word & What Fraud Victims Should Do Instead
-

 Education4 days ago
Education4 days agoDivine Light Academy: Schools, Coaching Institute & Spiritual Platform Explained
-
 Technology3 days ago
Technology3 days agoNational AIDS Council: Role, Countries, HIV Programs & Global Impact
-
 Blogs1 week ago
Blogs1 week agoKoriandri: Complete Guide to Koriandri Uses, Benefits, Growing, and Culinary Applications
-
 Blogs4 days ago
Blogs4 days agoAbbey Woodworking 2026: 165+ Years of Benedictine Craftsmanship, Furniture, and Monastery Tradition
-
 Home Improvement1 week ago
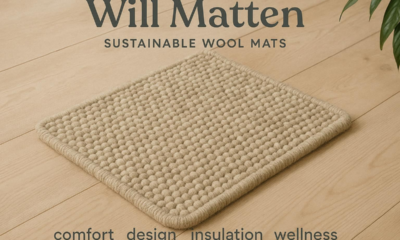
Home Improvement1 week agoWollmatten: Sustainable Wool Mats for Comfort, Design, Insulation & Wellness

